What if the file you need is already on the server, but your playbook still can’t access its content? You can connect to the host and copy files. You can even run commands on it. But the moment you need to read a file from a remote system directly into your playbook, things get tricky. That’s where most people start searching for Ansible Slurp.
The Ansible Slurp module is not for moving files. It is there to pull file content from a remote host into memory. So you can use it inside your playbook. This is quite useful when you have to inspect configs, extract values, and make decisions based on file data.
In this article, we are going to understand Ansible Builtin Slurp and will also compare Ansible Slurp vs Fetch.
Let’s go together!
What is Ansible Slurp?
Ansible offers the Slurp module to read files from remote systems. The Ansible Slurp module does the following things:
- Reads a file from a remote machine
- Encodes its content in base64
- Returns it inside a variable
Slurp doesn’t save the file locally. It loads the contents into the memory.
When to Use Ansible Slurp?
You should use Ansible Slurp when:
- You need to read the file content for logic
- You want to extract values from config files
- You need temporary access to file data
- You don’t want to store the file locally
You should avoid it for large files.
Basic Ansible Slurp Example
Here is a basic and simple Ansible Slurp example in action for you:
- name: Read remote file
hosts: all
tasks:
- name: Slurp file content
ansible.builtin.slurp:
src: /etc/hostname
register: file_data
- name: Show decoded content
debug:
msg: "{{ file_data.content | b64decode }}"What is happening here:
- The file is read from the remote system
- Content is base64 encoded
- We decode it using b64decode
How Ansible Slurp Works Internally?
You should understand the internal working of Ansible slurp to avoid mistakes. Here is the step by step working:
- Firstly, the file is accessed on a remote host
- Then the content is encoded in base64
- After that, the encoded string is returned
- Finally, you decode it in the playbook
These steps help explain why memory usage matters when using the Ansible Slurp module.
Working with JSON or Config Files
You can use Slurp to read structured data.
- name: Read JSON config
ansible.builtin.slurp:
src: /etc/app/config.json
register: config_file
- name: Parse JSON
set_fact:
config_data: "{{ config_file.content | b64decode | from_json }}"Now you can use config_data inside your playbook.
Ansible Slurp vs Fetch: Major Differences
| Feature | Slurp | Fetch |
|---|---|---|
| Purpose | Read content | Copy file |
| Storage | Memory | Local disk |
| Encoding | Base64 | No encoding |
| Use case | logic processing | file transfer |
Common Mistakes to Avoid
Here are some of the common mistakes you should avoid with Ansible Slurp:
Ise for Large Files
Slurp loads data into the memory. If you use it for large files, it can break down performance.
Forget to Decode
You always have to decode the content. Because it is always base64 encoded.
Use it instead of fetch
If you require a file locally, slurp is not the right option.
Conditional Logic Based on File Content
- name: Read config file
ansible.builtin.slurp:
src: /etc/myapp/config.conf
register: config_file
- name: Check value
debug:
msg: "Feature enabled"
when: "'enabled=true' in (config_file.content | b64decode)"Considerations for Performance
If you are using ansible.builtin.slurp, you have to keep these things in your mind:
- Avoid large files
- Limit usage in loops
- Decode only when you need
- Monitor memory usage in big playbooks
Real Use Cases of Ansible Slurp
1. Validate configuration values
Check if a setting exists before restarting services.
2. Read logs remotely
Extract error patterns without copying full log files.
3. Security auditing
Verify permissions or sensitive configuration values.
4. Conditional automation
Run tasks based on file content.
Best Practices
- always decode content immediately
- use it only for small files
- combine with filters like
from_jsonorfrom_yaml - use clear variable names for readability
Role of CyberPanel in The Automation Ecosystem
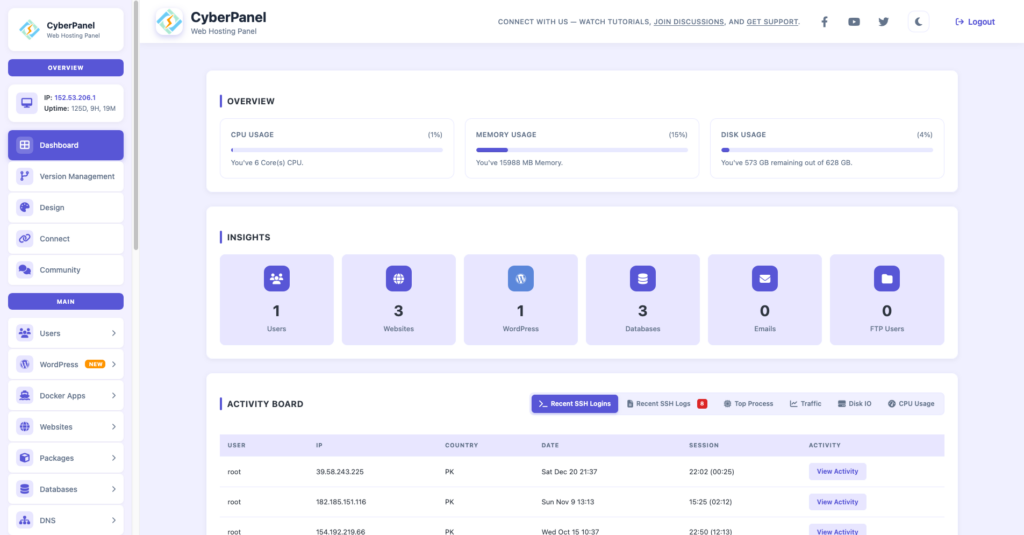
CyberPanel is a free and open-source web hosting control panel. It lends a hand in infrastructure where Ansible is the main tech.
When Ansible is used for automation and configuration, CyberPanel is the one that takes care of:
- web servers
- hosting environments
- SSL certificates
- application deployment layers
How it communicates with Ansible slurp
Here is a simple example of a workflow:
- Ansible slurp gets the Nginx configuration file
- identifies the errors
- CyberPanel is used to restart or manage the services visually
. The two tools complement each other in infrastructure management. The integration is very typical in production hosting environments.
Conclusion
Ansible Slurp does not serve the purpose of a file transfer tool. It is a simple method of incorporating remote file content into your automation logic.
On the one hand, it makes configuration validation, log reading, and conditional automation very easy. On the other hand, it unnecessarily increases memory usage when it is used inappropriately.
Indeed, the main feature of ansible.builtin.slurp is to take remote file content and make it available for your playbooks to use without disrupting the automation flow.
First, try using Slurp to work on a small configuration file in your setting. Decode it, check the values, and run a task based on the condition. After you know how it acts in real workflows, you can safely and effectively integrate it into more advanced automation with a minimum-effort.
FAQs
Does Ansible Slurp work on binary files?
Yes, it works with binary files because it encodes everything in base64. However, decoding binary data inside playbooks is rarely useful unless you are processing it programmatically.
Can Ansible Slurp replace configuration management tools?
No. Slurp is not a configuration management tool. It is a utility module used for reading file content. It complements automation but does not manage configurations itself.
Is Ansible Slurp secure for sensitive files?
Slurp itself does not encrypt data beyond base64 encoding. Security depends on your Ansible transport (SSH). For sensitive files, ensure secure connections and avoid logging decoded content.