It is risky to manage firewall rules manually. One simple mistake in a command might cause you to lose access to your own server. When the infrastructure enlarges, it becomes more challenging to maintain security across multiple machines.
That’s why Ansible UFW is really changing the game.
Instead of setting up firewalls one at a time, you can use Ansible to automate the whole process. Whether you want to let the SSH port through, close some ports, or maintain a set of rules that are the same everywhere, UFW Ansible is the tool that will allow you to do it in a safe and fast manner.
This article will show you how to run Ansible with UFW, set rules without mistakes, and manage firewalls automatically in a neat and scalable way.
What Is Ansible UFW?
Ansible is a great tool that lets you run server commands and other system tasks automatically on many computers at the same time.
Uncomplicated Firewall (UFW) is a straightforward firewall software that is found on many Linux machines.
Ansible UFW refers to using Ansible to control the settings of the UFW firewall without doing it manually.
This helps you:
- apply consistent firewall rules
- reduce manual errors
- manage multiple servers easily
- improve security
What Is Ansible Builtin UFW Module?
Ansible Builtin UFW is a native Ansible module to handle UFW rules.
What It Can Do
- allow or deny ports
- enable or disable firewall
- manage rules safely
- reset configurations
Basic Example:
- name: Allow HTTP
ansible.builtin.ufw:
rule: allow
port: 80How to Use Ansible UFW Module
Using the Ansible UFW module is simple and safe.
Example: Enable Firewall
- name: Enable UFW
ansible.builtin.ufw:
state: enabledExample: Allow HTTPS
- name: Allow HTTPS
ansible.builtin.ufw:
rule: allow
port: 443Ansible UFW Allow SSH Example
One of the most important rules in SSH access. Here is an example of ‘Allow SSH’
- name: Allow SSH
ansible.builtin.ufw:
rule: allow
name: OpenSSHBest Order for UFW Automation
When you are using UFW Ansible, follow this safe order:
- allow SSH
- allow required ports, i.e., HTTP, HTTPS
- enable firewall
Advanced Ansible UFW Example
- hosts: servers
tasks:
- name: Allow SSH
ansible.builtin.ufw:
rule: allow
name: OpenSSH
- name: Allow HTTP
ansible.builtin.ufw:
rule: allow
port: 80
- name: Allow HTTPS
ansible.builtin.ufw:
rule: allow
port: 443
- name: Enable UFW
ansible.builtin.ufw:
state: enabledOutput:
- SSH access secured
- web traffic allowed
- firewall enabled safely
Benefits of using UFW with Ansible
Ansible UFW cuts down on work, and it is a solid choice.
Consistency
Rules stay the same on every server you manage.
Safety
It probably cuts down on human errors you might make by hand.
Speed
You can spin up settings across many machines in minutes.
Scalability
Grows well whether you’ve got one box or a hundred.
Common Mistakes to Avoid
Don’t fall into these traps when using Ansible UFW.
Not Allowing SSH First
That could leave you locked out – no way in.
Enabling Firewall Too Early
You should define rules before turning the firewall on.
Hardcoding Rules
Use variables for flexibility.
Ignoring Testing
You must test first, even if it’s just one server.
Role of CyberPanel in Firewall Management
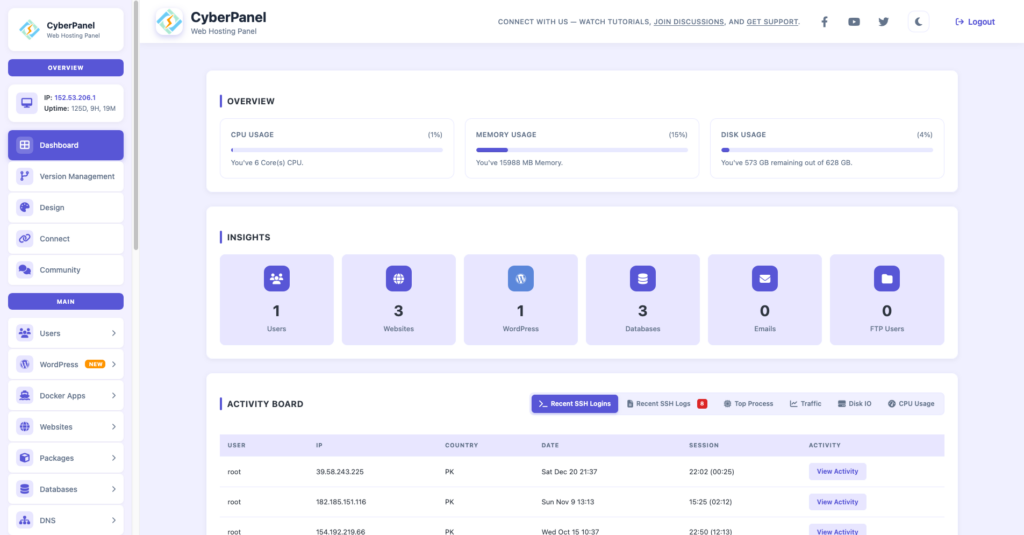
CyberPanel is a free and open-source web hosting control panel. It can help out with UFW when managing servers.
It covers:
hosting setups, watching activity logs, area handling, and SSL certificates.
The firewall keeps security tight with UFW, although CyberPanel runs apps and services smoothly.
Making sure your system stays protected isn’t just about rules – it’s about what happens when things go wrong, too.
Conclusion
Firewall management matters, mainly for servers. Ansible UFW lets you set rules automatically, cuts down on mistakes, and keeps systems safe without fail.
If you know how the Ansible Builtin UFW module works and follow safe steps like allowing SSH with UFW, your setup becomes dependable and strong.
Set up your first Ansible UFW playbook now, automate firewall rules across all servers so they stay consistent and protected.
FAQs
Is UFW a suitable solution for production?
Absolutely! UFW is a very popular solution for managing firewalls that is simple and effective, particularly on Ubuntu servers.
Can I disable UFW through Ansible?
Yes. You may disable UFW by setting state: disabled in the Ansible module.
Does Ansible UFW support IPv4 and IPv6 rules?
Yes. Both IPv4 and IPv6 can be managed with UFW by enabling IPv6 in the configuration.